Secure Spread Spectrum Watermarking of Images
1. Introduction:
The theory behind the scheme can be found in
[1]. Many of the implementation details have been taken from [3]. Here
I present a synopsis of the various tools developed by me and the
tests performed.
2. Tools developed :
- Generating the watermark (gen_wm tool)
: This tool generates a random sequence of numbers which
constitute a signature based on various parameters entered by the user
such as embedding strength (alpha), mean value, deviation, length and
a seed value for the random number generator. If no seed value is
given then the a auto seed consisting of a combination of process id
and current time is used making each sequence practically unique in
itself. All other factors if left unspecified have default
values.
- Embedding the watermark (wm_e tool)
: This tool embeds the above generated watermark into the
image. The watermark gets embedded in side a broad spectrum of the
lower frequencies in the DCT of the image. The method used to compute
DCT is based on using an auxillary function along with the
FFT.
- De-embedding(extracing) the watermark
(wm_d tool) : This tool extracts the embedded watermark
from the watermarked image into a signature file. Since Cox's method
is not blind it requires the presence of the original image along with
the embedding parameters alpha and length to extract the
watermark.
- Comparing two watermarks (cmp_wm tool)
: This tool compares two watermarks, the original and the
extracted,and primarily outputs the 'normalized correlation' [2]. The tool also
outputs the corrsponding input and output watermark sequences if so
desired by the user.
- Comparing two images (cmp_img tool)
: This tool compares two images, the original and the
watermarked. It can output the difference image and/or various
statistics like Peak Signal Noise Ratio(PSNR),Root Mean Square
Error(RMS), Mean Square Error(MSE) values. These statistics can be
used to determine quantitaively and the difference image qualitatively
how much the watermarking process alters the original image. All the
operations can be done in the DCT domain as well using the same tool.
- A text menu wrapper (water tool) :
All the above tools have command line interfaces, this tool provides a
text menu based interface to the above tools.
3. Tests :
The tests are really robustness checks , used to
determine how the watermarking scheme resists various kinds of
attacks.The tests were done on two sets of watermarks with alpha
factors 0.3(low strength embedding) and 0.5(medium strength
embedding). The test procedure in general was as follows:
- Generate and embed a watermark into the image.
- Perform various operations on the watermarked image to alter it (the attack).
- Extract the watermark from the altered watermarked image.
- Compare with the original watermark and original image.
The primary measure of confidence here is the
correlation output by the cmp_wm tool. Though I have generated
the difference images in the image and DCT domains for each test but
here I present only the statistical outputs because of storage
restrictions. All the tests have been run in batch modes using
scripts.
NOTE: Originally the tests were done on PGM images,
I have converted them to JPEG because the browser does not display PGM
images.
3a. The Normal test:
Here the whole test has been done without
altering the watermarked image i.e. these are the results observed if
no attempt is made to corrupt the watermarked image. I have also shown
the difference image which gets generated in both the
cases.

|

|

|
|
Original Image
|
Watermarked Image
Alpha 0.3
|
Watermarked Image
Alpha 0.5
|
|
Correlation
|
0.7062627
|
0.9056124
|
|
Other Statistics
|
PSNR: 40.4494 dB
RMSE: 2.4142
MSE: 5.86328
|
PSNR: 28.6921 dB
RMSE: 9.37427
MSE: 87.877
|
|
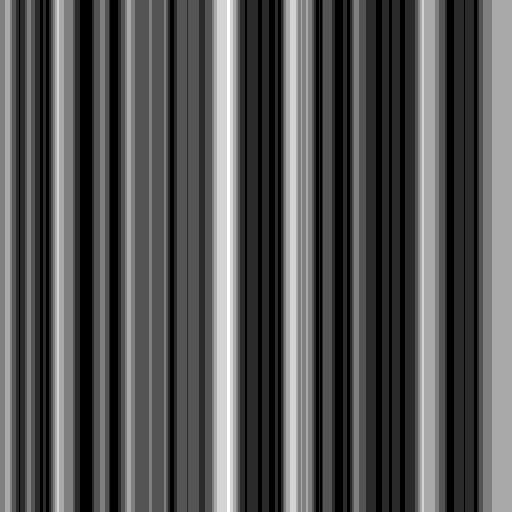
|

|
|
Difference Image
(Image domain)
Alpha 0.3
|
Difference Image
(DCT domain)
Alpha 0.3
|
Difference Image
(Image domain)
Alpha 0.5
|
Difference Image
(DCT domain)
Alpha 0.5
|
3b. The Median Filter Test:
Here the watermarked image was subjected to a 3x3
Median Filter.

|

|

|
|
Original Image
|
Altered Watermarked Image
Alpha 0.3
|
Altered Watermarked Image
Alpha 0.5
|
|
Correlation
|
0.30938035
|
0.382867
|
|
Other Statistics
|
PSNR: 31.7709 dB
RMSE: 6.57647
MSE: 43.25
|
PSNR: 27.037 dB
RMSE: 11.342
MSE: 128.641
|
3c. The Histogram equilization test:
Here the watermarked image was subjected to global
histogram equilization.

|

|

|
|
Original Image
|
Altered Watermarked Image
Alpha 0.3
|
Altered Watermarked Image
Alpha 0.5
|
|
Correlation
|
0.43318069
|
0.72988371
|
|
Other Statistics
|
PSNR: 19.4453 dB
RMSE: 27.1816
MSE: 738.839
|
PSNR: 18.8571 dB
RMSE: 29.0862
MSE: 846.008
|
3d. The Noise test:
Here the watermarked image was corrupted using the
noisify
filter from GIMP.

|

|

|
|
Original Image
|
Altered Watermarked Image
Alpha 0.3
|
Altered Watermarked Image
Alpha 0.5
|
|
Correlation
|
0.22867523
|
0.42767831
|
|
Other Statistics
|
PSNR: 20.1623 dB
RMSE: 25.028
MSE: 626.4
|
PSNR: 19.6649 dB
RMSE: 26.5031
MSE: 702.417
|
3e. The Crop test:
Here a part of the watermarked image was cropped and
used to replace that portion from the original (non-watermarked) image,
which was then used to extract the watermark.

|
|
 
|
|
Original Image
|
Altered Watermarked Image
&
Cropped portion of the watermarked image
Alpha 0.3
|
Altered Watermarked Image
&
Cropped portion of the watermarked image
Alpha 0.5
|
|
Correlation
|
0.47348723
|
-0.079599761
|
|
Other Statistics
|
PSNR: 47.4594 dB
RMSE: 1.08036
MSE: 1.16718
|
PSNR: 31.9548 dB
RMSE: 6.43872
MSE: 41.4571
|
3f. The JPEG test:
Here the watermarked image was subjected to lossy
JPEG compression and then that image was used to extract the watermark.

|

|

|
|
Original Image
|
Alteread Watermarked Image
Alpha 0.3
|
Altered Watermarked Image
Alpha 0.5
|
|
Correlation
|
0.64820298
|
0.87809159
|
|
Other Statistics
|
PSNR: 35.928 dB
RMSE: 4.0751
MSE: 16.6064
|
PSNR: 28.1869 dB
RMSE: 9.93564
MSE: 98.7169
|
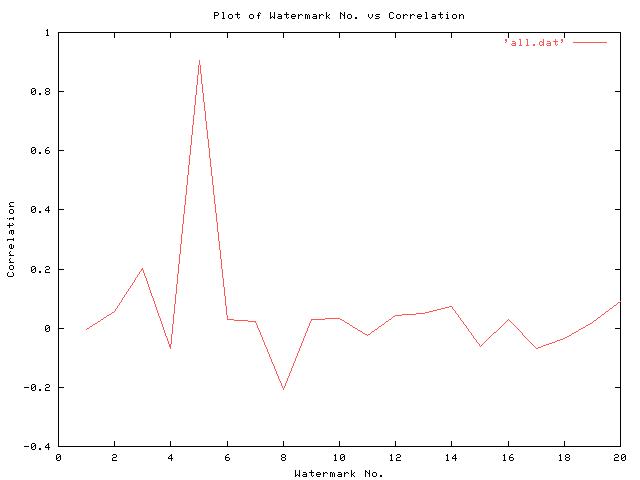
3g. The False Positives test:
Here the 20 random watermarks were generated out of
which only one was actually embedded in the image. The response of the
watermark detector i.e. the correlation obtained by comparing
the extracted watermark with each of the above watermarks was plotted and
is shown below.
4. Conclusions :
- The watermarking method is quite robust against the attacks tested for.
- The watermarking procedure though simple is quite secure.
- Higher Alpha values always give better correlation hence have a
higher embedding strength, but induce more error in the image.
- The closer the watermarked image is to the original the higher is
the PSNR value and lower is the RMSE and MSE values and vice-versa,
hence these can be used as quantitative measures to check how the
watermarking process effects the original image.
- The possibility of false positives coming up is very very less.
- The watermark cannot be destroyed without significantly affecting the image itself.
5. Improvements & further study possible :
- A scheme of watermarking using a block DCT would be computationally more efficient.
- More tests should be conducted to verify strictly the robustness of the above method.
- As newer compression schmes (like JPEG2000) are using the Wavelet
Transform rather than DCT, Wavelet based watermarking schemes could be
investigated.
- A study of proving ownership claims based on watermarks would be interesting.
- A study of the application of watermarking to other media such as
video, audio & graphical data sets would be interesting.
- A study of the field of Steganography or Information Hiding would be very interesting.
|
Page last updated on 28 January, 2004.
|
 AT cse.iitd.ac.in AT cse.iitd.ac.in
|
© Parag Chaudhuri , 2009
|
|
|























 AT cse.iitd.ac.in
AT cse.iitd.ac.in